How zero-access analytics improve ROI for common data initiatives and expand addressable markets by streamlining processes and eliminating regulatory roadblocks.
You’ve heard about the need to get involved in business strategy discussions to help drive business value and growth. But how can you avoid stepping out of your lane or being told not to slow things down?
In our last blog, we discussed how zero-access data analytics solutions like Duality’s can be used to first address the exploding risks seen with third-party data arrangements.
This new capability begs the question, “If we can apply zero-access data analytics to reduce risk in using sensitive data, can it also be used in a way that drives growth or improves ROI on business initiatives?” Such a platform provides data and security teams a force-multiplier for their data-driven initiatives in two ways:
- Improving ROI by identifying data-driven initiatives wherein security, compliance, or privacy requirements demand time and/or money.
- Unlocking growth by focusing on initiatives that are limited or slowed by complexities found in compliance, security, or privacy; e.g., data monetization.
Table Stakes: Communicating Value
In order for CISOs, CPOs, and CDAOs to become growth drivers and leaders, they must communicate effectively. This means using language that starts with business value and is supported by use cases and technical capabilities. By shifting to this order, conversations with non-technical leadership will be more engaging versus asking for approval of a foregone conclusion explained by technical capabilities and use cases alone. For example, Gartner notes, “Top performing CISOs regularly meet with three times as many non-IT stakeholders as they do IT stakeholders.” Rob Woods puts it succinctly: “Security teams cannot do everything,” and continues to point out the obvious opportunities in working closely with other departments. Security teams’ work adds value when others understand and make use of it.
Discovering Opportunities for Improved ROI
The following questions can help CISOs, CPOs, and CDAOs identify key areas where ROI and value can be enhanced with zero-access data analytics:
- Is a manual process to protect sensitive data used or required (e.g., data de-identification)?
- Are lengthy legal and compliance processes needed in order to access or analyze a data set?
- Are data and analytics protections technically enforced, or only organizationally enforced?
- Do any methods used for data privacy and protection require trusting a third party?
- With whom do we have data sharing agreements?
- How are we monetizing data or analytics? If not, would we like to?
But, what if you’re not the one with those answers? Ideally, identifying where complex processes and technologies exist is as easy as searching through a data inventory or a recent audit report. However, we all know that such documents are notoriously difficult to create and maintain due to the speed and sprawl of data across cloud services. Additionally, such documentation may not reflect current initiatives, goals, or wishes. Here are two ways to find out what’s being done or considered:
- Start with corporate objectives. It may go without saying, but always align with corporate objectives. This will help appropriately prioritize and position discussions for maximum impact and support. Follow the trail from strategic objectives to the data-tactics required. This will provide a short list of high-profile, data-driven initiatives.
- Ask the users. Driving growth needs to be inclusive, so having strong relationships and regular conversations outside your specific team is highly recommended. Data Teams should have a good idea of where such processes are being used because they’re the primary players/users. The Privacy Team may also have records of where such processes exist
The ‘Low-Hanging Fruit’: Death to De-identification
Out with the old, in with the new. If an organization is using de-identification in any operation, there’s a high likelihood of being able to improve its ROI. Why? De-identification is a process-driven tactic that removes specific data points making it hard – but not impossible (not GDPR compliant) – for someone with access to the dataset to identify a particular person or group therein. Whether by tokenization or removal, this comes at a cost found in time to value, quality of insights, and the utility of the data overall. There is significant time spent between the data owners, data analyzers, and privacy/security experts in determining that the dataset meets requirements while still providing a minimal level of value to the analyzers. In healthcare, the method is called expert determination which adds even more time and cost to the effort. In any case, when valuable data context is removed from a dataset, the value and quality of insights that can be derived are also reduced. This leaves many wondering, if insights aren’t actionable, what’s the point?
In a recent example, Colin Woodard, Director of Nationhood Lab, mentioned the detrimental impact of working with restricted data by saying, “For privacy reasons the [CDC] suppresses county data with low numbers, which wreaks havoc on efforts to calculate rates for less numerous ethno-racial groups.” This is not uncommon. In addition, such subsets are limited in utility since they can’t be linked with other, disparate datasets. This means that a de-identified dataset must be valuable enough on its own, which is problematic in the face of the growing need for collaboration among data-driven enterprises.
Virtually any operation utilizing de-identification processes will benefit from zero-access analytics by:
- Enhancing security and reducing risk (deidentification does not satisfy anonymization).
- Reducing time to value & preparation costs by streamlining processes.
- Improving the quality of insights by working with full data context.
- Improving data utility since disparate datasets can be linked.
- Remove or severely limit the movement of data prior to use.
The values in modernizing such a process for today’s data-driven enterprises should be quite clear. Most of the work will be aligning the many stakeholders involved.
Data Monetization
Data monetization: Two words that are sure to send chills down the spine of those responsible for data governance, protection, security, or privacy. To explain the adrenaline rush caused by such an initiative, we must mention the core prerequisites versus the operational difficulties. First, the organization needs to have its data under control and organized. Commonly, the answer will vary based on the datasets and data types being discussed. Wrangling data sprawled across services and clouds is daunting even without regulations in mind. Once the baseline preparation is done (or nearly there), we can begin building a plan to operationalize data monetization as a new revenue stream with security, privacy, and compliance requirements met or exceeded. Today, the status of data monetization efforts in data-driven organizations typically falls under one of the following three descriptions:
- An established line of business.
- Done, but in limited circumstances.
- A desired future.
Established Line of Business – Improving ROI and TAM
If selling data to 3rd parties is already an established line of business (or your only line of business), there’s an opportunity to both improve ROI and expand the total addressable market (TAM) using a zero-access approach. For example, sensitive datasets are often sold in their entirety rather than accessed through a portal. The customer will receive and host this data (note* a risk, time, and cost increase) on their end before making use of it. This is largely driven by client requirements to keep their analytical needs and insights private – without visibility from the vendor – due to security, regulatory, or intellectual property concerns. This approach can be cost prohibitive, reduces the quality of insights, and may limit the geographies in which such a service can be offered due to data localization and transfer laws. Using a zero-access analytics platform allows vendors to satisfy data localization and transfer laws, reduce costs of service delivery, setup time, and total cost of ownership (TCO) while satisfying the needs of their clients. By reducing costs and complexities, data vendors can expand to new geographies and customer segments, driving profitability and overall revenue growth with the addition of wholly new audiences.
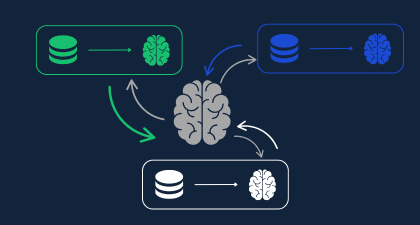
Duality provides options to query, analyze joined/linked data sets, or run models on encrypted data. The above shows the Duality Query flow, where sensitive query parameters are hidden from commercial data vendors.
Special Cases or a Desired Future – Operationalizing a Data Service
Almost all organizations have data that is valuable to other organizations, an opportunity many are beginning to explore. The “data gold mine” realization is often followed by enthusiasm. Unfortunately, the momentum is lost in the fray of complexities and requirements identified by security, data, IT, and privacy/legal teams. These complexities can limit data monetization to strategic relationships or special circumstances only, if at all. A zero-access analytics platform removes arguably the most significant complications in setting up a scalable operation; data access, protection, security, and privacy. With a platform that checks all boxes by default, all that remains is to have customers install a piece of software to begin gaining value from your new, or newly expanded, line of business.
Two Birds, One Stone
If you’re looking for a way to impact growth from the risk side of the aisle, a platform like Duality’s provides many such opportunities while simultaneously improving overall risk posture. Using a zero-access analytics platform eliminates risk from sensitive data use, improves ROI for data initiatives, and can generate more revenue by turning valuable wish lists into realities.
By introducing a zero-access analytics platform in the context of improving ROI and unlocking growth-driving initiatives, risk leaders like the CISO, CPO, and CDAO earn their place at the table as growth leaders rather than simply being service department heads.
What’s Next?
In blog 1, we covered how to eliminate risk from common, 3rd party data arrangements to prove that data in-use can be secure. We’ve now discussed how to improve ROI for existing, but complex, data operations. Next, we’ll talk about paths to strategic growth and innovation by exploring options that either couldn’t be done or haven’t been considered.
Book a demo with us to learn more.