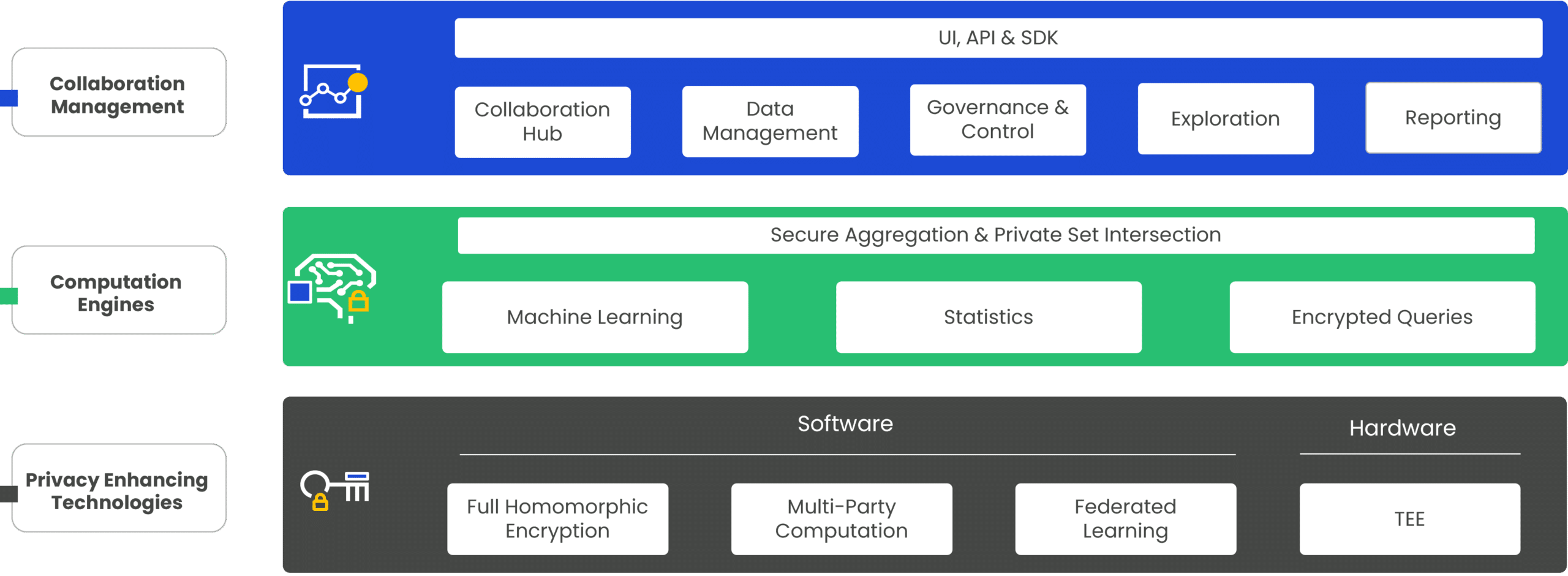
Facilitate data collaboration across trust boundaries, geographic regions, and disparate infrastructures while maintaining data privacy, confidentiality, and security. Duality operationalizes multiple advanced privacy and security technologies into computational, collaboration, and governance layers. This enables us to offer a range of use cases while satisfying global regulatory requirements and protecting intellectual property.
We enable organizations to securely collaborate on sensitive data and models, allowing you to quickly access data that wasn’t available, or was available but in limited capacity.
Our Secure Collaborative AI solution allows clients to test and license model usage without relying on ‘trust’, giving them built-in governance controls, enforcement, and reporting to know that their data is safe.
Our secure data technologies allow you to be a data service provider and monetize sensitive information securely while complying with data compliance regulations.
The Duality privacy-preserving data collaboration platform leverages cryptographic methodologies and hardware technologies tightly woven into computation, collaboration, and governance layers. These enhance several Privacy Enhancing Technologies (PETs) useful in secure data collaboration while complying with data privacy, security, confidentiality, and regulatory requirements.
Securely share insights by performing privacy-preserving queries on decentralized data sets.
Duality uses the leading open source for fully homomorphic encryption (aka FHE), empowering data teams and data owners with tools for secure collaboration on sensitive data.
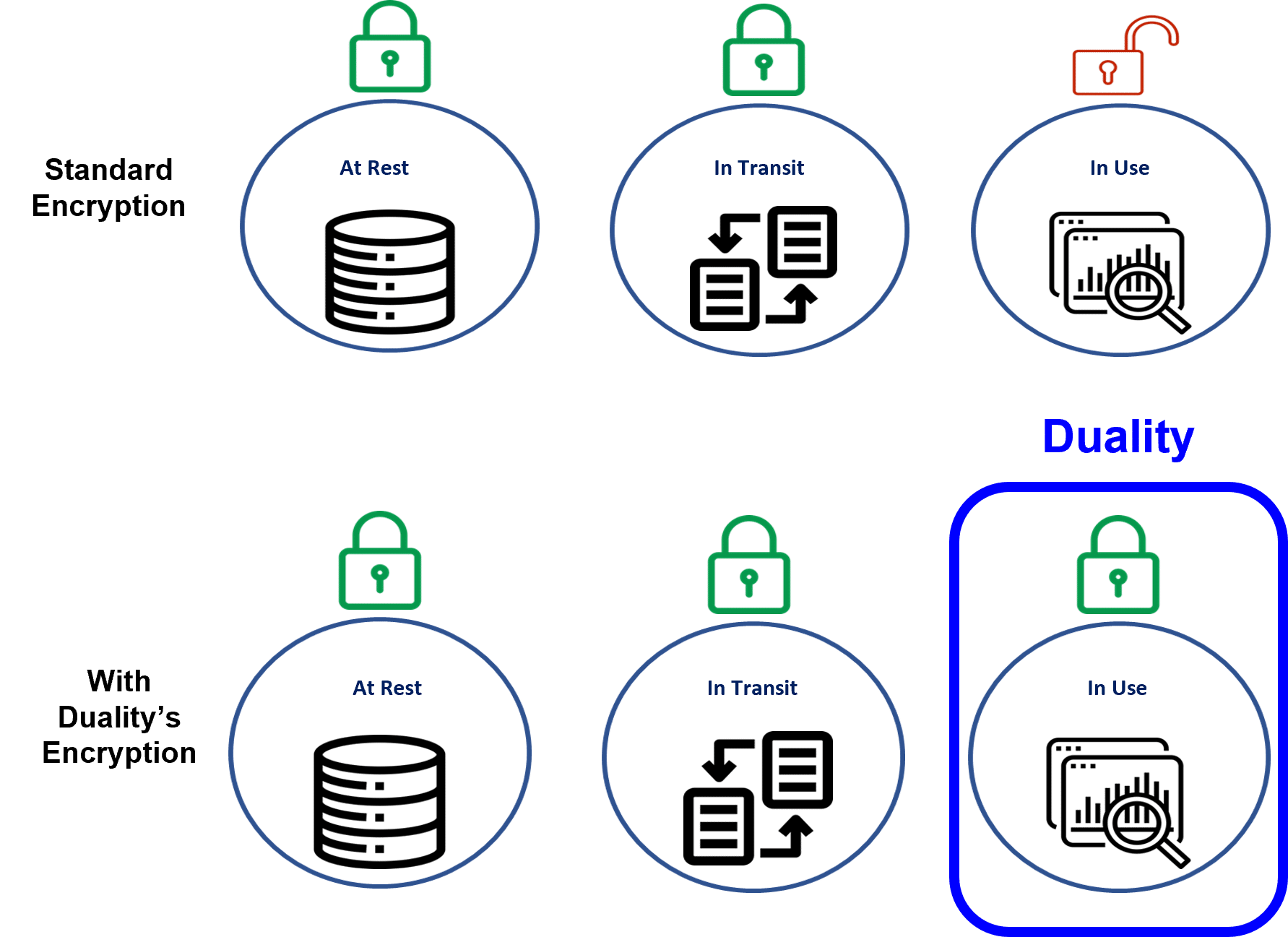
Privacy enhancing technologies (PETs) protect data in use. Data has three basic states: at rest, in transit, and in use. Organizations that handle sensitive data, such as personally identifiable information (PII) or confidential material, typically encrypt or otherwise protect that data while it is being stored (at rest) or when it is being transmitted (in transit)–. However, there have been no truly good options to technically protect data in-use. When the data is processed, analyzed, or manipulated in any way, it must be decrypted. This means every use and access point to data, is a data risk. Because of this, data access has been and will be a major challenge in establishing efficient data flows necessary for data-driven innovation and growth, especially true when involving data hunger AI/ML models.
Duality leverages cryptographic methodologies to enhance multiple PETs allowing complex computations to be run on data while the data and model themselves are hidden and secure from data breaches. So, users can select the most appropriate technology(s) to meet their requirements both in use and policy.
The Duality platform has built-in interfaces for machine learning training and inferencing. This gives you the option of training and serving models on sensitive data or sensitive models while ensuring both data and model IP are not exposed. This includes LLM fine runing as well as LLM serving and RAG flow.
The Duality query engine allows multiple organizations to collaborate on decentralized data by performing privacy-enhanced SQL-like queries. The query and results are secured by homomorphic encryption, ensuring that the underlying data remains within the owner’s environment and the query is being encrypted so the data owner is not exposed to the object of investigation.
Provides a toolset for multiple datasets across various accounts as part of the collaboration network. From data ingestion, through data preparation, to performing analysis on the data, our platform enables data pre-processing and schema alignment between end users.
Provides users with full management of data access controls, and their security strategy, allowing each participant in the collaboration network to define exactly what is shared, and with whom, using best practices for data privacy that meet and exceed industry standards.
Includes tools that help users start their exploratory data analysis by using sample data, schema info, and other tools in a way that does not expose any sensitive data but allows the user to gain insights and validate hypotheses.
Delivers extensive reporting options for auditing and log analysis, enabling thorough oversight and transparency throughout the collaboration process.
Empower your organizations to share and analyze encrypted data using Duality’s Privacy Enhancing Technologies (PETs) such as Fully Homomorphic Encryption, Federated Learning, Trusted Execution Environment, and more…
Enable privacy-preserving data collaborations across your entire financial ecosystem.
Protect patient data across your healthcare network through privacy-preserving collaborations.
Utilize data collaboration to drive digital marketing efforts with creativity and accuracy.
Maximize the value of sensitive, regulated, or confidential data.
Utilizing fully homomorphic encryption (FHE) and advanced privacy-enhancing technologies, Duality enables you to perform secure machine learning, analytics, and SQL-like queries on encrypted data. This allows you to acquire and use data without being an expert in cryptography or privacy engineering while maintaining the confidentiality of any sensitive information.