In the first three parts of this series, we spotlighted massive spending in healthcare mergers and acquisitions and the goals therein, understood the players involved, and explored some of the key challenges. Mainly, how does one support greater use of data while simultaneously improving the protections of it? This is the part where objectives are tossed over the fence to their Chief Digital Officer (CDO) and say “you can do all this by yesterday with no additional budget or resources, right? Great!” As usual, this is where the real lift begins – and it’s always easier said than done. This blog explores the impact of data privacy in mergers and acquisitions in healthcare.
Scoping the Work
The CDO takes business objectives and coordinates across multiple teams and budgets to implement and operationalize solutions to achieve them. Generally speaking, there are five key departments with whom the CDO will need to coordinate human, capital, and operational resources: (1) security, (2) data, (3) privacy/governance/legal, (4) business (5) IT/infrastructure. Notice that the CDO must coordinate, not command – they don’t own these departments or their budgets. To describe such a digital transformation and maturity exercise as daunting would be a massive understatement.
Post-M&A, this enterprise now consists of an insurance organization, care delivery organization, and pharmacies. Good, those are three key data owners that must collaborate to achieve the defined business goals. But, once the ink dries, press releases published, and congratulations shared, the CDO faces a mountain of work to coordinate potentially 15 departments across geographies and separate lines of business. The teams don’t know each other. There is no data collection standard. We’re talking about a multi-cloud effort to unite petabytes of information from many owners for various data teams across many purposes. This is why the work will likely be tackled one use case at a time. With all of that on the table, where is the starting point?
Here’s a more formal list of key areas to consider:
- Ensure data privacy and security
- Integrate systems and data
- Establish a data governance program
- Build a unified user experience
- Create an analytics strategy
- Develop a data-driven culture
Each of the items above is loaded and we don’t have time to dig into each. At the risk of oversimplifying, let’s focus on the pieces involving sensitive data and segment it into three buckets:
- Data at rest
- Data in-motion
- Data in-use
Furthermore, here are the primary questions that must be answered regarding said data:
- Where is it?
- Which type of data is it?
- How is it protected?
- Who has or needs access, when, and why?
None of the above are simple to answer. The unmitigated data sprawl across cloud services haunts CISOs to this day. But, we have seen progress in technology that enables operationalizing discovery and classification so policies and guardrails can be enacted for the data itself (at-rest) rather than at a system level. After all, you can’t protect what you don’t know.
Data in-transit is the simpler of the three data types to cover and we’ll assume that the means to securely send data is covered. However, data in-use remains an unfortunate, accepted chink in our armor, largely addressed by work arounds. Processes and solutions to make JITAM (just-in-time access management) manageable are great in reducing the risk by moving away from permanent, role-based access policies and adding a ‘per session’ layer of authorization. For our CDO, this is massively problematic as all of the major business objectives require significant increases in data use, and therefore exposure and risk. This means data will need to be moved to where the right people can extract gold from the raw data ore. Fortunately, this is where the long overdue introduction of privacy tech comes into play.
What are Privacy Enhancing Technologies and how do they help the CDO?
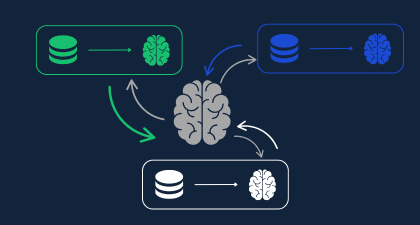
Privacy-enhancing technologies (PETs) are those that focus on ensuring that data can be shared or used while satisfying security and privacy requirements, and some even ensure that data can be analyzed without being tied to an individual. One of the unique aspects of leading-edge privacy technology as compared to security and governance tech is that it isn’t strictly used for “revenue protection”, but rather “revenue generation”. Good privacy solutions can be the difference between having or not having data for analysis – and therefore, between having actionable versus inactionable insights. Fortunately for the CDO and the relevant stakeholders, Duality Technologies has a platform purpose-built for preserving the privacy and security of data while in use.
Illustrative Private Technology: Homomorphic Encryption & More
Common approaches to securing data include zero-trust and JITAM, but wouldn’t “zero-access” be best? As impossible as that sounds, we agree. Which is exactly why Duality has built a zero-access data analytics platform. The journey began with technology called fully homomorphic encryption (FHE). The technology is quantum safe, and allows data teams to analyze and query data where it resides, while remaining encrypted. No direct access to the data means no exposure. No exposure, means no worries. Hakuna matata.
That may sound too good to be true, but you don’t have to trust us, verify it yourself.
Duality has made the underlying engine an open source project called OpenFHE, which Google’s Privacy and Security Engineering team announced use of back in August 2022. It’s been in use by US government agencies and various financial and healthcare organizations for over 10 years. Making our tech open-source is a critical component of maintaining its goals in being a privacy preserving, secure collaboration technology.
While trade-offs exist in comparison to analyzing data in the open, it’s far better than not analyzing data at all – often the case with privacy, security, and competitive considerations in play. Plus, like all technology, the speed continues to accelerate on a month-to-month basis opening the doors to more use cases. And although FHE is where Duality got its start, the platform employs multiple PETs to accommodate more advanced workflows and uses. Essentially, the location of the data and the analyzers is no longer a major hurdle. Not only does this seriously change the speed of innovation, it finally brings the data stewards to the table in strategies and tactics to enable business growth (shift-left anyone?).
Were the Mergers and Acquisitions even necessary?
Valid question. The answer is “most likely” because the list of benefits in these acquisitions do go beyond data collaboration, albeit a primary mission directive. But as the value of data in our economy continues to grow, we’re already hearing discussions in M&A strategies to consider purchases based on data alone. However, platforms like Duality’s will open up the doors to data monetization revenue streams without the prohibitively complex operations they require today. Many businesses are sitting on valuable data they pay to protect but can’t utilize to its full potential.
The progress of privacy and security regulations and technology over the next 2, 5, and 10 years will force organizations to move away from risk-accepting BAAs and toward technology solutions that address “incidental access”. Fortunately, organizations that use compliance as a minimum rather than a maximum already have such solutions today. All organizations should know that if they’re struggling to link, query, or analyze data because of privacy and security regulations or growing corporate risk concerns, there are better, faster, less risky, and affordable options coming out of the privacy space.
Conclusion
Healthcare companies know that the path to solving the world’s biggest health issues requires better data-driven insights. To achieve this, they need to aggregate and link disparate data sets from across the entire patient health journey. The massive spending in healthcare M&A leads to that end, and is pushing organizations to move to new levels of data maturity and innovation that we should all be excited to see. But, nothing is free. To minimize the risks and avoid the negative consequences of such data aggregation and use, we must architect such solutions with security and privacy by design. Which, is exactly what we’ve done.