Cloud data governance is often framed as a maturity journey: discover your data, classify it, assign ownership, and apply policies. That model provides a useful starting point, but it does not reflect how data actually behaves in modern cloud environments. Data is continuously moving across services, regions, and organizations. It is accessed by pipelines, APIs, machine learning systems, and external collaborators. A governance model that focuses primarily on visibility cannot control this level of complexity.
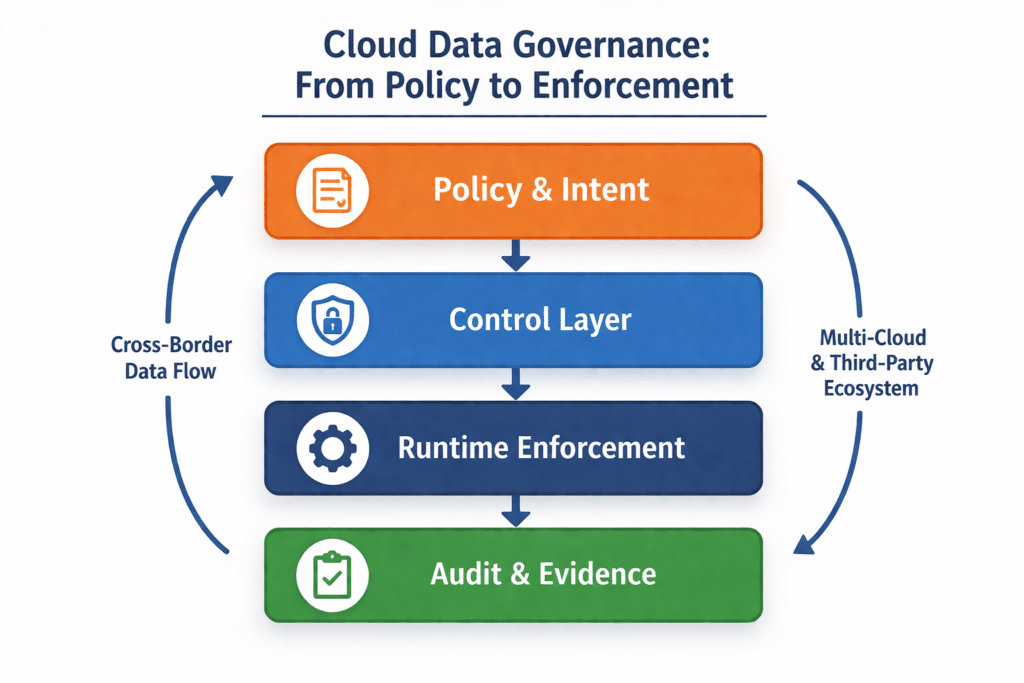
Cloud data governance becomes meaningful only when policy is enforced at the moment data is accessed or processed. This is where security experts consistently identify gaps. Organizations invest heavily in cataloging and classification, yet struggle to enforce access controls, constrain usage, and produce verifiable evidence under audit conditions. The issue is not awareness of data, it is the inability to operationalize governance across distributed systems.
This challenge becomes more pronounced in regulated industries. Financial services, healthcare, and public sector organizations must support cross-border data flows, third-party collaboration, and increasingly AI-driven processing. These use cases require balancing data utility with strict control over access, jurisdiction, and purpose. Achieving that balance requires treating governance as an architectural control system rather than a documentation exercise.
Why regulated environments expose governance gaps faster
Regulated industries surface weaknesses in cloud data governance earlier because their requirements extend beyond internal control. Financial institutions, healthcare providers, and public sector organizations operate under strict obligations that govern not only access, but also processing context, jurisdiction, and accountability. These environments require organizations to prove that controls are enforced continuously, not just defined.
In practice, this means governance must account for scenarios such as cross-border analytics, third-party data processing, and AI model training on sensitive datasets. Each of these introduces competing requirements: enabling data use while restricting exposure. For example, a healthcare provider may need to collaborate with an external analytics partner while ensuring patient data never leaves a specific jurisdiction or is accessed without strict controls.
This pressure reveals structural weaknesses in cloud data governance models. Systems that rely on static permissions, fragmented policy enforcement, or weak auditability quickly fail under regulatory scrutiny. As a result, regulated environments act as a forcing function, pushing organizations toward more integrated, enforceable, and evidence-driven governance architectures.
Why cloud data governance breaks in practice
Most cloud based data governance programs are designed to answer foundational questions about data inventory and ownership. These capabilities are necessary, but they do not address how data is used once it enters active workflows across cloud systems.
The core failure occurs when governance artifacts are not connected to enforcement layers. Policies, classifications, and ownership definitions exist in governance platforms, while enforcement is distributed across identity systems, storage services, analytics engines, and applications. This separation introduces inconsistencies that increase over time.
Several recurring failure patterns explain why data governance in the cloud struggles to deliver control:
- Policies are defined centrally but implemented inconsistently across cloud services
- Data classification does not trigger automated enforcement actions
- Governance does not extend to pipelines, APIs, or downstream systems
- Evidence of enforcement is incomplete or fragmented across tools
These issues are amplified by the dynamic nature of cloud infrastructure. Resources are provisioned programmatically, permissions evolve continuously, and data flows across systems at scale. Governance approaches based on periodic reviews or manual enforcement cannot keep pace.
A practical scenario highlights the problem. A dataset may be correctly classified and stored in a compliant environment. However, an automated pipeline may still export that data to another region or expose it to downstream systems without equivalent controls. The classification exists, but it does not influence behavior where it matters.
Governance fails when policy intent is not continuously enforced across every system interacting with the data.
Modern cloud data governance approaches address this by embedding policy into infrastructure. Identity systems, access controls, and processing layers become enforcement points, ensuring governance decisions are applied consistently across environments.
The access governance gap most teams underestimate
One of the most significant gaps in cloud data access governance is the treatment of non-human identities. While organizations typically manage user access through reviews and certifications, machine identities often operate with broader permissions and less oversight.
In cloud environments, workloads such as data pipelines, microservices, APIs, and AI models frequently outnumber human users. These systems access data continuously and at scale. If they are not governed effectively, they introduce a large and often invisible risk surface.
Common weaknesses include:
- Service accounts with long-lived credentials and excessive privileges
- Automated workflows that bypass governance controls
- APIs exposing sensitive data without contextual authorization
- Machine learning pipelines accessing raw data without restriction
These issues persist because governance models were originally designed around human access patterns. They assume access decisions can be reviewed periodically, which does not align with automated systems making real-time decisions.
Modern cloud platforms are evolving toward context-aware access control. Access decisions are based on attributes such as workload identity, execution environment, geographic location, and declared purpose. This allows organizations to enforce policies dynamically and reduce reliance on static permissions.
For example, a data processing job may be granted access to sensitive data only if it runs in a trusted environment, uses approved code, and operates within a defined region. If any condition changes, access is denied automatically. This aligns governance with real-world system behavior.
Another critical consideration is identity lifecycle management. Machine identities should be short-lived, scoped to specific tasks, and continuously validated. Long-lived credentials introduce persistent risk, particularly in automated environments where misuse may not be immediately visible.
Why metadata without enforcement is not governance
Metadata plays a central role in cloud data governance by providing visibility into data assets, lineage, and classification. However, metadata alone does not enforce control. It describes the state of data without influencing behavior unless integrated into enforcement systems.
Many organizations can answer what data they have and where it resides. Fewer can demonstrate how governance policies affect access, processing, and usage in practice. This distinction defines the maturity gap in data governance in the cloud.
For governance to be effective, metadata must drive system behavior. A classification label should directly influence:
- Access control decisions based on sensitivity and context
- Data masking or tokenization during processing
- Retention and deletion policies
- Cross-border data transfer restrictions
- Eligibility for analytics and model training
Without these connections, governance remains observational. It provides insight but does not reduce exposure.
A common failure scenario involves sensitive data being correctly classified but still broadly accessible. Analysts, applications, or partners may access the data without additional restrictions because classification is not integrated into access policies.
Cloud data governance in multi-cloud and cross-border environments
Multi-cloud environments increase governance complexity because each provider implements identity, access control, logging, and data protection differently. Even when policy intent is consistent, enforcement mechanisms vary across platforms.
This creates a translation challenge. Organizations must map governance policies across multiple environments while maintaining consistency. Without a unified control model, policy drift becomes inevitable.
Cross-border data governance introduces additional constraints. Data sovereignty requirements extend beyond storage location to include processing, administrative access, and legal jurisdiction. Governance must ensure compliance regardless of where data is accessed or processed.
Key considerations include:
- Enforcing residency and jurisdictional constraints across regions
- Controlling administrative and privileged access
- Managing encryption keys in line with regulatory requirements
- Restricting data movement between jurisdictions
- Producing auditable evidence of compliance
A common challenge arises when data is stored in one region for compliance but processed in another for performance. Without strict controls, this can violate regulatory requirements despite apparent compliance at the storage layer.
Effective cloud based data governance requires a portable policy model. Policies should be defined independently of any single platform and then mapped to provider-specific controls. This ensures consistency while leveraging native capabilities.
Centralized vs decentralized cloud data governance models
Organizations must decide how to structure governance across teams and environments. Centralized and decentralized models each offer advantages, but both introduce limitations when applied in isolation.
Centralized governance ensures consistency and simplifies audit processes. Policies are defined and enforced uniformly, reducing ambiguity. However, this model can limit flexibility and slow down delivery in dynamic environments.
Decentralized governance allows teams to implement policies aligned with their specific use cases. This improves agility but increases the risk of inconsistency and reduced visibility across the organization.
A federated model provides a balanced approach by combining centralized standards with decentralized execution.
| Model | Strength | Limitation | Best Fit |
| Centralized | Consistency and auditability | Reduced agility | Highly regulated environments |
| Decentralized | Flexibility and speed | Increased drift risk | Product-driven organizations |
| Federated | Balance of control and adaptability | Requires coordination maturity | Global enterprises |
Effective governance aligns centralized policy definition with decentralized execution and automated evidence collection.
Where privacy-enhancing technologies fit
Privacy-enhancing technologies (PETs) extend cloud data governance by enabling controlled data use without exposing raw data. They are particularly valuable in cross-border collaboration, regulated analytics, and AI development.
These technologies address scenarios where access control alone is insufficient. Instead of granting access, they enable computation under controlled conditions.
Key PETs include:
- Confidential computing, which protects data during processing
- Differential privacy, which limits disclosure risk in outputs
- Federated learning, which enables distributed model training
Each technology introduces trade-offs. Confidential computing depends on trusted hardware environments. Differential privacy reduces data fidelity in exchange for privacy guarantees. Federated learning reduces data movement but introduces risks related to model leakage.
These trade-offs must be evaluated within the governance model. PETs are most effective when they reduce exposure while preserving required functionality.
Privacy-enhancing technologies reduce exposure pathways and enable secure collaboration across jurisdictions.
Building a control model that survives audits
A cloud data governance model must demonstrate enforceability and produce verifiable evidence. Regulatory scrutiny focuses on how controls operate in practice.
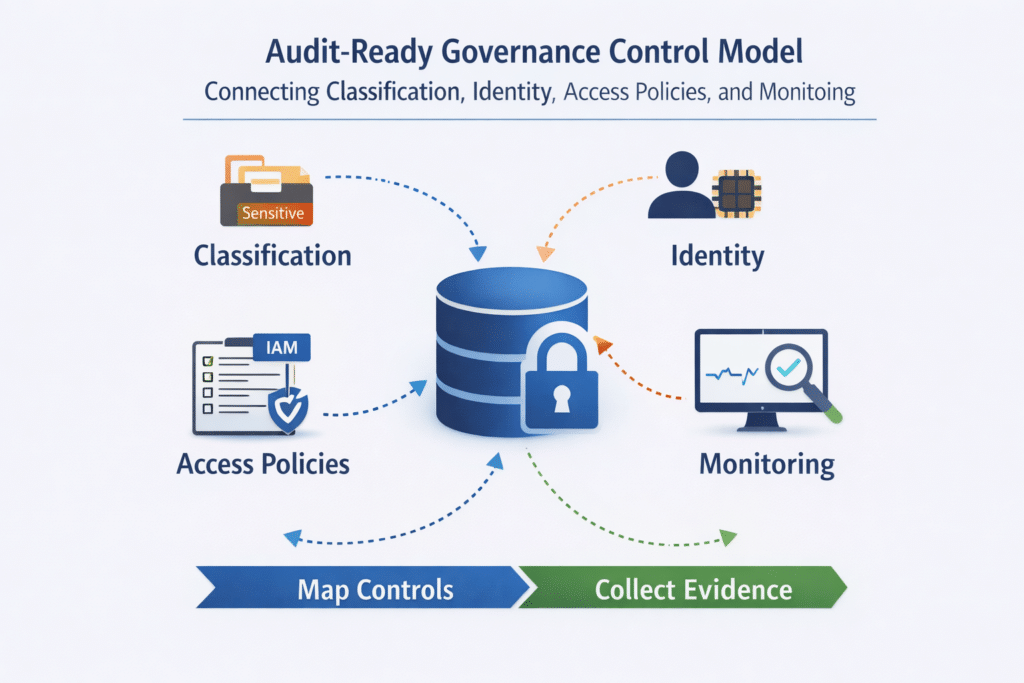
Organizations must be able to show:
- Data classification linked to enforceable policies
- Identity governance across users and workloads
- Context-aware access control decisions
- Oversight of administrative and provider access
- Compliance with data sovereignty requirements
- Comprehensive audit logging and traceability
These capabilities require an integrated control architecture. Governance must connect identity, data platforms, infrastructure, and monitoring into a cohesive system.
A typical audit scenario illustrates this requirement. Regulators may request evidence showing how access to sensitive data is controlled and monitored. This requires linking classification, identity policies, access logs, and enforcement mechanisms into a single, coherent narrative.
Organizations with fragmented systems struggle to produce this evidence. Those with integrated governance architectures can demonstrate compliance efficiently and consistently.
Conclusion
Cloud data governance challenges stem from gaps between policy definition and enforcement. Organizations often achieve visibility into their data but fail to operationalize controls across distributed environments.
Security experts consistently highlight the same issues: weak governance of machine identities, lack of enforcement tied to metadata, inconsistent multi-cloud controls, and limited support for secure collaboration.
Addressing these gaps requires a shift toward enforceable, evidence-driven governance. This includes integrating policy with runtime controls, adopting context-aware access mechanisms, and leveraging privacy-enhancing technologies where appropriate.
Organizations that make this shift improve both compliance and operational capability. They gain the ability to manage sensitive data securely while enabling innovation across cloud environments.