Data sovereignty laws have evolved from a niche compliance concern into a primary architectural constraint for any organization operating across borders. In 2026, regulatory fragmentation is accelerating, and businesses must navigate a growing patchwork of national rules that directly influence how data is stored, processed, and shared.
The complexity is both legal and deeply technical. These laws shape cloud infrastructure decisions, determine where AI models can be trained, and restrict how datasets can move between jurisdictions. Organizations that fail to account for these constraints early often face costly redesigns or regulatory penalties later.
This guide provides a country-by-country breakdown of data sovereignty laws, explains their effect on modern systems, and outlines practical strategies for maintaining compliance without sacrificing performance or innovation.
What Are Data Sovereignty Laws and Why Do They Matter?
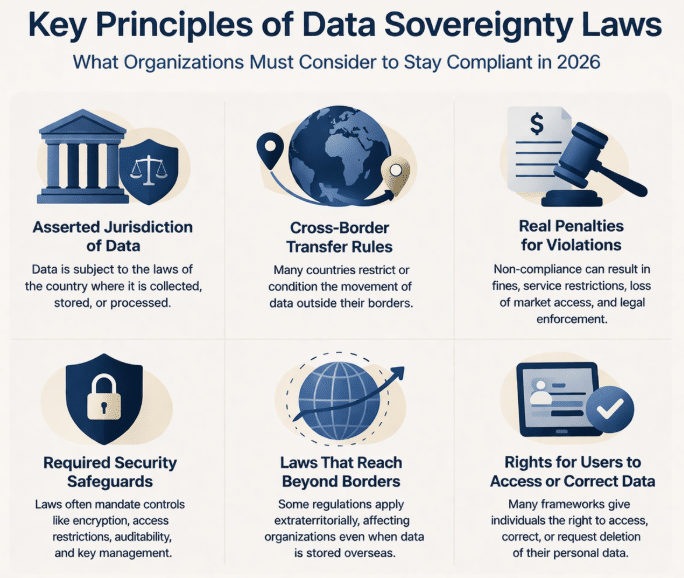
Data sovereignty laws define how data is governed based on geographic location. In practice, this means that data is subject to the legal framework of the country where it is collected, stored, or processed. Many of these laws introduce data localization requirements, forcing certain types of data to remain within national borders.
These laws have gained importance due to three structural shifts in the digital ecosystem:
- Governments are treating data as a strategic national asset.
- Cloud computing has obscured physical data location.
- AI systems require large-scale, cross-border datasets.
As a result, organizations must now treat jurisdiction as a first-class design variable. This affects a wide range of teams, including compliance, engineering, security, and data science.
From a systems perspective, data sovereignty laws directly determine:
- Where data can be stored and processed
- Whether cross-border transfers are permitted
- How encryption and key management must be implemented
- Which authorities can legally access the data
Ignoring these constraints often leads to architectures that cannot be deployed globally without significant rework.
Data Sovereignty Is an Architecture Problem and a Legal Risk
Most organizations treat data sovereignty laws as compliance constraints. In practice, they also dictate system design affecting data pipelines, cloud topology, and AI workflows. Teams that fail to account for this early often face costly re-architecture later.
A Deeper Dive into Structural Shifts
1. Governments Are Treating Data as a Strategic National Asset
Historically, a nation’s strategic assets were physical, things like natural resources, trade routes, and industrial capacity. In the 21st century, data has been elevated to this level. Here’s why:
- Economic Competitiveness: Data is the “new raw material” of the digital age. Governments recognize that the massive datasets generated by their citizens and industries can fuel innovation, boost productivity, and create new economic sectors. By controlling this data, they aim to foster local technology industries and ensure that the economic benefits are realized domestically, rather than flowing to foreign entities.
- National Security: In an interconnected world, data provides critical intelligence. It can reveal insights into a nation’s infrastructure, economic vulnerabilities, and population dynamics. Governments are increasingly concerned that if this data is stored abroad, it could be accessed by foreign adversaries for espionage or political leverage.
- Policy and Governance: Governments rely on data for everything from designing effective public services to managing economic policy. As one Australian government policy states, information is a “key strategic asset…as important as budget, property and equipment.”
2. Cloud Computing Has Obscured Physical Data Location
The fundamental design of cloud computing is to abstract away the physical location of infrastructure. While this provides enormous benefits in terms of scalability and resilience, it creates a direct conflict with geographically-based legal systems.
- The “Borderless” Illusion: For years, the appeal of the cloud was its seemingly borderless nature. You could store your files “in the cloud” without needing to know, or caring, where the physical servers were located. However, all data is physically stored somewhere, and that “somewhere” determines which country’s laws apply.
- Jurisdictional Conflicts: The distributed nature of the cloud means data can be moved and copied across multiple locations without the user’s direct knowledge. This creates legal ambiguity. For example, data belonging to a European citizen might be stored on a server in the United States, making it subject to both EU privacy laws (like GDPR) and U.S. government access laws (like the CLOUD Act). This conflict is a primary driver for data residency rules.
- Loss of Control: When data is handed over to a public cloud provider, organizations lose direct control over the physical infrastructure making it difficult to guarantee compliance with national laws that require data to be stored within a specific jurisdiction. As a result, major cloud providers now offer regional data centers to help customers meet these data residency requirements.
3. AI Systems Require Large-Scale, Cross-Border Datasets
The rise of AI has dramatically increased the demand for vast and diverse datasets. This has created a new set of challenges in the context of data sovereignty.
- The Need for Diverse Data: AI models, particularly in fields like machine learning, are only as good as the data they are trained on. To be effective and unbiased, they require massive, diverse datasets that often span multiple countries and demographics. For example, an AI model for climate change prediction trained only on data from one region may not be accurate for others.
- Data Fragmentation: Data sovereignty laws, by their very nature, create “data silos,” restricting the free flow of information across borders. This fragmentation makes it difficult to aggregate the large-scale datasets needed to train powerful AI models.
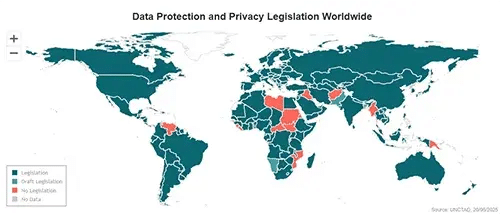
Global Overview of Data Sovereignty Laws
Countries enforce data sovereignty through different regulatory models, each with distinct implications for system design. Understanding these models is essential for building scalable and compliant infrastructure.
There are three dominant approaches shaping global data sovereignty requirements:
- Open transfer with safeguards: Data can move freely if protections such as contractual clauses or adequacy agreements are in place.
- Conditional localization: Certain industries or data types must remain within national borders.
- Strict localization: Data must be stored and processed domestically, with minimal transfer allowances.
These models are increasingly overlapping as countries refine their policies. Many jurisdictions are moving toward hybrid frameworks that combine localization with conditional transfers, creating additional complexity for global operations.
Country-by-Country Breakdown of Data Sovereignty Laws
European Union (GDPR)
The European Union’s GDPR remains the most influential framework for data sovereignty laws. Instead of enforcing strict localization, it primarily regulates how data can leave the region. Organizations must ensure that any transfer meets strict protection standards.
The impact of rulings such as Schrems II has been significant. Companies are now required to assess foreign surveillance risks and implement safeguards that go beyond contractual agreements. This has transformed cross-border data transfer into an ongoing compliance process instead of a one-time setup.
United States (CCPA and Sectoral Laws)
The United States follows a decentralized approach, combining state-level regulations like CCPA with sector-specific laws such as HIPAA and GLBA. This creates flexibility alongside inconsistency.
While localization is generally not required, laws like the CLOUD Act introduce jurisdictional complexity. Data stored abroad may still be accessible to U.S. authorities, which can conflict with foreign sovereignty requirements.
Brazil (LGPD)
Brazil’s LGPD closely aligns with GDPR principles while allowing more flexibility in international data transfers. Organizations must demonstrate adequate protection, though strict localization is not broadly enforced.
However, enforcement is evolving, and regulators are increasingly focusing on how organizations manage cross-border data flows, especially in regulated industries.
China (PIPL and Data Security Law)
China enforces one of the strictest data sovereignty regimes globally. Sensitive data must be stored domestically, and cross-border transfers require government approval.
This creates a clear architectural requirement: organizations operating in China must maintain separate, localized infrastructure. This often results in parallel systems that are difficult to integrate with global environments.
India (Digital Personal Data Protection Act)
India is adopting a hybrid model that allows cross-border transfers while retaining the ability to restrict certain jurisdictions. The direction of policy suggests increasing localization over time, particularly for sensitive sectors.
Russia
Russia mandates strict localization for personal data and enforces compliance aggressively. Non-compliant organizations risk service blocking, making this one of the most operationally impactful regimes.
Comparative Summary of Data Sovereignty Laws
| Region | Localization Requirement | Transfer Flexibility | Enforcement Strictness |
| EU | Conditional | Moderate | High |
| US | Low | High | Medium |
| Brazil | Conditional | Moderate | Medium |
| China | Strict | Low | Very High |
| India | Emerging | Moderate | Increasing |
| Russia | Strict | Low | High |
Fragmentation Is the Real Risk
The biggest challenge is the inconsistency across jurisdictions, rather than any single regulation. Systems that are compliant in one region may be non-compliant in another, forcing organizations into fragmented architectures.
Which Countries Have the Strictest Data Sovereignty Laws?
Strictness in data sovereignty laws is best understood through enforcement intensity and operational impact, as well as the legal wording itself. China and Russia are the most restrictive because they combine mandatory localization with strong enforcement and limited transfer mechanisms.
The European Union, while not mandating localization, imposes continuous compliance obligations that can be equally demanding. Organizations must constantly validate transfer mechanisms and monitor legal exposure.
Enforcement Drives Real Risk
While organizations often focus on legal text, enforcement truly determines the real-world impact. A moderately strict law with aggressive enforcement can be more disruptive than a stricter law with limited oversight.
How Data Sovereignty Laws Affect Cloud Computing and Storage Decisions
Cloud computing was designed to abstract infrastructure, but data sovereignty laws reintroduce geography as a critical constraint. Organizations must now align cloud architecture with jurisdictional requirements.
This affects several core design decisions:
- Selecting cloud regions for data residency
- Designing redundancy without violating localization rules
- Restricting administrative access across jurisdictions
- Managing encryption keys within specific legal boundaries
Multi-Region Cloud Does Not Guarantee Compliance
Deploying across multiple cloud regions alone does not ensure compliance. Organizations can still violate data sovereignty laws without jurisdiction-aware access controls and key management.
A common pattern is the creation of regional data silos. Data is processed locally, with only aggregated insights shared globally. This reduces compliance risk at the cost of increased system complexity and operational overhead.
How Data Sovereignty Laws Impact AI Model Training and Collaboration
AI systems depend on diverse datasets, but data sovereignty laws restrict how these datasets can be combined. This creates fragmentation that can reduce model accuracy if not addressed properly.
To overcome this, organizations are adopting distributed approaches such as federated learning. These methods allow models to be trained across multiple jurisdictions without moving raw data.
However, these approaches introduce trade-offs:
- Increased system complexity and orchestration overhead
- Higher latency during training and inference
- New governance challenges for model validation
Sovereignty Is Reshaping AI Architecture
Centralized data lakes are becoming incompatible with global regulations. Distributed, privacy-preserving architectures are emerging as the default for scalable AI systems.
What Happens When Organizations Violate Data Sovereignty Laws?
Violations of data sovereignty laws can result in significant financial penalties and severe operational consequences.
Organizations may face:
- Multi-million dollar fines under frameworks like GDPR
- Suspension of cross-border data transfers
- Forced data repatriation
- Service shutdowns in specific regions
These outcomes can disrupt business continuity and require immediate architectural changes, often under regulatory pressure.
Industry Impact: Healthcare, Finance, and Government
Highly regulated industries experience the strongest effects of data sovereignty laws because they handle sensitive and mission-critical data.
Healthcare organizations must ensure patient data remains protected within jurisdictional boundaries. Financial institutions face additional requirements related to systemic risk and transaction security. Government entities often require full localization and strict access controls.
These sectors are leading adopters of advanced compliance technologies because the cost of failure is significantly higher.
How Privacy-Enhancing Technologies Help Organizations Comply with Data Sovereignty Laws
Privacy-enhancing technologies (PETs) offer a sophisticated solution to the challenges of data sovereignty. Instead of just focusing on where data is stored, PETs fundamentally change how data is processed, allowing for cross-border collaboration and analysis while keeping the underlying data secure and compliant. They provide a scalable way to meet data sovereignty requirements while preserving data utility.
Here is a deeper look at the key PETs and how they work:
Federated Learning: For Decentralized Model Training
Federated learning directly addresses data localization requirements by reversing the traditional data analysis paradigm. Instead of bringing data to a central model, it brings the model to the data.
- How it Works:
- A central server distributes a global AI model to local servers in each jurisdiction (e.g., a server in Germany and another in Brazil).
- The model is trained locally using only the data within that jurisdiction. The raw data never leaves its geographic or network boundary.
- Each local server sends back only the mathematical insights, the learned “updates” or “gradients”, to the central server.
- The central server aggregates these updates to improve the global model without ever accessing the raw data.
- Compliance Benefit: This method is inherently compliant with data residency laws because the sensitive data remains within its required jurisdiction at all times.
Homomorphic Encryption (HE): For Computation on Encrypted Data
Homomorphic Encryption is a groundbreaking cryptographic technique that allows mathematical operations to be performed directly on encrypted data.
- How it Works:
- Data is encrypted at its source before it is moved or shared.
- This encrypted data can then be sent to a central server or another partner for processing.
- The server can perform computations (like training an AI model or running statistical analysis) on the data while it is still encrypted.
- The result of the computation is also encrypted and can only be decrypted by the original data owner.
- Compliance Benefit: HE allows organizations to transfer and process data across borders because the sensitive information is never exposed. It remains an unintelligible ciphertext to anyone without the decryption key, mitigating the risks associated with foreign government access or breaches.
Trusted Execution Environments (TEEs): For Secure Processing
TEEs are secure, isolated hardware enclaves (like Intel SGX or AMD SEV) that protect data and code while they are being used.
- How it Works:
- A TEE creates a verifiable “secure black box” on a processor.
- Data from one or more parties is loaded into this enclave.
- Inside the enclave, the data is processed. Crucially, the code and data are isolated from the rest of the system, including the host operating system and even the cloud provider’s administrators.
- Compliance Benefit: TEEs create a neutral, protected ground where data from different jurisdictions can be securely combined for joint analysis. This provides technical assurance that data access is restricted according to policy, helping to satisfy strict cross-border access rules.
Differential Privacy: For Protecting Individual-Level Data
Differential Privacy is a mathematical framework that enables the sharing of aggregate insights from a dataset while protecting the privacy of individuals within it.
- How it Works:
- Before the results of a query or analysis are released, a carefully calibrated amount of statistical “noise” is added.
- This noise is large enough to make it impossible to determine whether any single individual’s data was included in the calculation, but small enough to ensure the overall result remains useful and accurate.
- Compliance Benefit: While not a direct solution for data localization on its own, differential privacy is often combined with other PETs. It provides a strong, mathematically provable guarantee that no personal information can be leaked from the output of a cross-border analysis, helping organizations comply with the core principles of data protection frameworks like GDPR.
By combining these technologies, organizations can build modern, secure data architectures. They can collaborate on a global scale, unlock the full value of their distributed data, and innovate with AI all while maintaining compliance in a world of fragmented data sovereignty laws.
Conclusion
Data sovereignty laws are fundamentally reshaping how organizations design systems, manage data, and deploy AI. The regulatory environment is becoming more fragmented, requiring compliance to be embedded directly into architecture.
Organizations that succeed will treat sovereignty as a primary design constraint and a legal consideration. By combining region-aware infrastructure with privacy-enhancing technologies, they can maintain both compliance and innovation in a rapidly evolving landscape.