What Is Data Sovereignty Under GDPR?
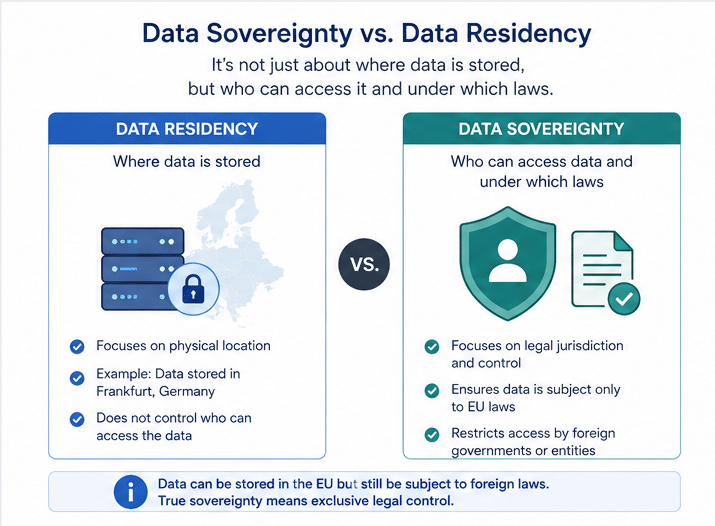
Many people hear “data sovereignty” and think it’s simple: just keep EU data physically stored on servers within the European Union. But that’s a dangerously incomplete picture. In reality, data sovereignty under GDPR is a far more profound legal and technical principle that governs how personal data is accessed, processed, and, most importantly, controlled regardless of where it sits.
At its heart, this concept is about jurisdictional control. The General Data Protection Regulation (GDPR) is designed to ensure EU citizens’ data remains shielded by EU law, even when it’s handled by third parties or crosses borders. If that data becomes subject to foreign laws that can override GDPR’s robust protections, then its sovereignty is compromised, even if the servers are in Frankfurt or Dublin.
This distinction was thrown into sharp relief by the Schrems II ruling. It forced a critical shift in thinking, moving beyond pins on a map. Now, compliance teams must scrutinize not just infrastructure location but also legal exposure, vendor ownership, and every possible access pathway. A dataset stored in the EU but accessible to a US-based parent company, for instance, may fail to meet today’s sovereignty standards.
Why Data Sovereignty Matters More After Schrems II
The Schrems II decision fundamentally reshaped how regulators interpret GDPR data sovereignty. It established that data transfers to countries without “adequate” protections require strict safeguards and even then, those safeguards must be effective against foreign government access.
The ruling emphasized that contractual mechanisms like Standard Contractual Clauses (SCCs) are insufficient on their own. Organizations must assess whether the receiving country’s legal framework allows government surveillance that conflicts with GDPR rights. If it does, additional technical protections are required or the transfer must stop.
This has elevated sovereignty from a compliance checkbox to a continuous risk assessment process. Companies must now demonstrate that data remains protected in practice, not just in theory. This includes evaluating encryption strength, access controls, and whether any party can decrypt or access the data under foreign jurisdiction.
The Conflict Between GDPR and the US CLOUD Act
One of the most direct challenges to data sovereignty under GDPR comes from the US CLOUD Act. This US law grants American authorities the power to compel US-based technology companies to provide requested data, regardless of where that data is stored globally.
From a GDPR standpoint, this creates a legal paradox. EU personal data, even when stored securely in a European data center, could be lawfully accessed by a non-EU government without the safeguards or judicial oversight mandated by the GDPR. For any organization using a US-headquartered cloud provider, this conflict is not hypothetical; it’s an active risk. Your provider could be caught between contradictory legal obligations: a GDPR duty to protect the data and a CLOUD Act duty to disclose it.
| Aspect | GDPR Requirement | CLOUD Act Implication |
| Jurisdiction | EU law governs EU data | US law can apply extraterritorially |
| Access Control | Strict, rights-based access | Government access without EU safeguards |
| Compliance Burden | Data exporter must ensure protection | Provider may be forced to disclose |
This tension forces organizations to rethink vendor selection and architecture. It is no longer enough to choose a provider with EU data centers; legal exposure must be minimized at every layer.
Core GDPR Data Sovereignty Requirements
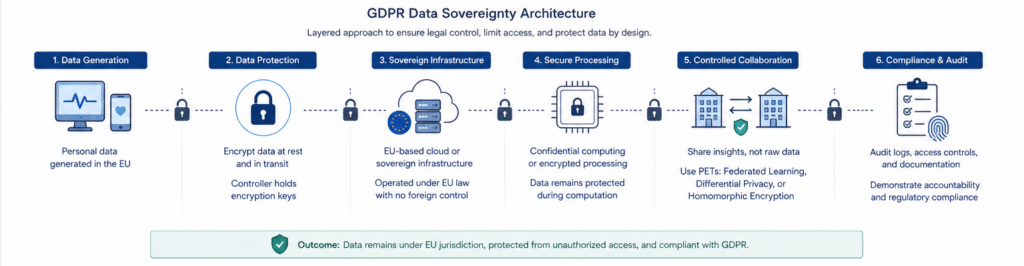
To truly meet GDPR’s sovereignty obligations, organizations need a multi-layered strategy of legal, organizational, and technical controls. These requirements aren’t found under a neat “sovereignty” heading in the regulation; instead, they emerge from the interplay of multiple GDPR provisions and subsequent regulatory guidance.
- Ensure Lawful Data Transfers: Go beyond just signing SCCs. You must conduct and document Transfer Impact Assessments (TIAs) to rigorously evaluate whether the destination country’s laws could compromise the data you’re sending.
- Enforce Strict Access Controls: Sovereignty applies within the EU, too. Data should only be accessible to authorized personnel under GDPR-compliant conditions. This means re-evaluating administrative privileges and shutting down any backdoors that could lead to unauthorized third-party exposure.
- Leverage Strong Encryption and Anonymization: Data should be rendered useless to anyone who isn’t authorized to see it. This is your most critical technical defense against interception or compelled disclosure by foreign authorities.
- Maintain Demonstrable Accountability: You must be able to prove your compliance. This requires diligent record-keeping of your processing activities, data flows, TIAs, and governance frameworks, ready to be presented to auditors or regulators.
How to Conduct a Transfer Impact Assessment (TIA) for GDPR Data Sovereignty
A Transfer Impact Assessment (TIA) is the mechanism that turns GDPR data sovereignty from a legal concept into an operational decision. After Schrems II, organizations are required to evaluate whether data transferred outside the EU remains protected in practice, not just under contractual terms. This means assessing both the legal environment of the destination country and the technical realities of how data is handled.
A proper TIA begins with understanding the nature of the data and the context of the transfer. Sensitive personal data, such as health or financial records, raises the risk threshold significantly, especially when processed in jurisdictions with broad surveillance laws. At the same time, organizations must evaluate who can access the data, including cloud providers, subprocessors, and government authorities. This is where many assessments fail, they focus on contractual safeguards but overlook actual access pathways.
The legal analysis must then examine whether the destination country provides enforceable rights equivalent to GDPR protections. If authorities can compel access to data without sufficient judicial oversight or redress mechanisms, the transfer may violate sovereignty requirements. This is particularly relevant in jurisdictions with extraterritorial laws that override contractual commitments.
However, legal analysis alone is not sufficient. Organizations must also assess whether technical safeguards such as encryption, pseudonymization, or distributed processing effectively prevent unauthorized access. If data can be decrypted or reconstructed by a third party, the safeguards may not meet regulatory expectations.
In practice, a TIA should lead to one of three outcomes:
- The transfer is acceptable with existing safeguards
- The transfer can proceed only with additional technical controls
- The transfer must be avoided entirely
The key insight is that a TIA is not a static document. It is a defensible position that regulators can challenge, requiring continuous reassessment as legal frameworks and threat models evolve.
Can You Use US Cloud Providers and Stay Compliant?
The short answer is yes but only under strict conditions. Using US-based cloud providers does not automatically violate GDPR data sovereignty, but it introduces significant risk that must be mitigated.
Compliance depends on whether the provider can ensure that EU data is not subject to conflicting legal obligations. This often requires implementing strong encryption where only the data controller holds the keys. If the provider cannot access the data in plaintext, the risk of unlawful disclosure is reduced.
However, this approach has limitations. Key management must be fully independent, and metadata or access logs may still be exposed. Additionally, regulators may scrutinize whether technical measures truly prevent access in practice.
Organizations increasingly explore “sovereign cloud” models, where infrastructure, operations, and legal control are fully localized within the EU. These models aim to eliminate foreign jurisdictional risk rather than mitigate it.
Key Management: The True Control Point of Data Sovereignty
Encryption is often touted as the panacea for data sovereignty challenges, but that’s an oversimplification. The crucial question isn’t if your data is encrypted, but who controls the keys. If a third party, like your cloud provider, can access or reproduce the keys, your data remains vulnerable to their legal obligations, and your sovereignty is merely an illusion.
This insight shifts the entire conversation from encryption algorithms to key management architecture. In many standard cloud environments, providers manage the keys, even when offering services like encryption “at rest” and “in transit.” From a GDPR sovereignty standpoint, this is the critical flaw. If that provider is subject to the CLOUD Act, they may be compelled to use those keys to decrypt and hand over your data.
To counter this, organizations are adopting architectures like Bring Your Own Key (BYOK) or, for even stronger guarantees, Hold Your Own Key (HYOK). In these models, the encryption keys are generated, stored, and managed exclusively by the data controller. In the most advanced implementations, the keys never leave a sovereign-controlled environment and are never exposed to the cloud provider, even during computation.
Regulators are increasingly focused on this point. They want to know if any entity outside of EU jurisdiction can realistically access the data. By externalizing and tightly controlling key ownership, you can build a powerful case that even if data is stored or processed on foreign-owned infrastructure, it remains cryptographically sealed and under your exclusive control.
Compliance Risks of Failing Data Sovereignty Requirements
Failing to meet GDPR data sovereignty requirements exposes organizations to multiple layers of risk. Regulatory penalties are the most visible, with fines reaching up to 4% of global annual turnover. However, the operational and reputational consequences are often more damaging.
Non-compliance can lead to enforced data transfer suspensions, disrupting business operations and partnerships. It may also trigger legal challenges from data subjects or advocacy groups, especially in sensitive sectors.
From a security perspective, weak sovereignty controls increase the risk of unauthorized access or data breaches. If data is exposed through foreign legal mechanisms, organizations may have limited recourse.
There is also a strategic risk. As regulators tighten enforcement, companies that fail to address sovereignty proactively may find themselves unable to scale or enter regulated markets.
Industry Impact: Healthcare, Finance, and Government
For highly regulated sectors, the implications of data sovereignty are not just a matter of compliance; they are foundational to their license to operate.
- Healthcare: Organizations must guarantee that sensitive patient data remains confidential. A sovereignty failure could lead to unauthorized access to medical records, eroding patient trust and violating specific healthcare data protection laws.
- Finance: Financial institutions are bound by strict rules on data integrity, security, and auditability. Any ambiguity around who can access transaction data or customer information creates unacceptable regulatory and security risks.
- Government: Public sector bodies have an absolute duty to maintain full control over citizen data. Here, data sovereignty is often intertwined with national security, making any foreign access a non-starter.
In these industries, getting sovereignty right isn’t optional; it’s a prerequisite for doing business.
How Privacy-Enhancing Technologies Enable Compliance
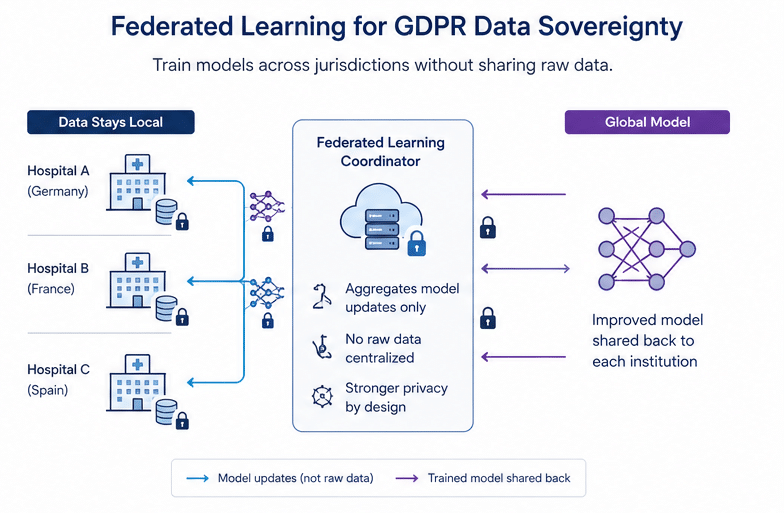
Privacy-enhancing technologies (PETs) are becoming essential tools for achieving GDPR data sovereignty without sacrificing functionality. These technologies allow organizations to process and analyze data while minimizing exposure and maintaining control.
A few approaches stand out:
- Homomorphic encryption enables computation on encrypted data, eliminating the need to decrypt it during processing
- Federated learning allows models to be trained across distributed datasets without centralizing raw data
- Confidential computing uses secure enclaves to protect data during processing
- Differential privacy ensures that outputs do not reveal sensitive individual information
These technologies shift the compliance model from “protect the perimeter” to “protect the data itself.” Even if data moves across systems or jurisdictions, it remains secure and inaccessible in meaningful ways.
PETs are governance mechanisms.
They allow organizations to prove that data cannot be misused, even under legal pressure.
Practical Architecture Patterns for Data Sovereignty
Implementing GDPR data sovereignty requires architectural decisions that align with both legal and technical constraints. There is no single solution, but certain patterns are emerging as effective.
| Pattern | Description | Sovereignty Benefit |
| Data Localization | Store and process data within EU boundaries | Reduces jurisdictional exposure |
| Sovereign Cloud | EU-operated infrastructure with no foreign control | Eliminates extraterritorial access risk |
| Encrypted Processing | Use PETs to process encrypted data | Prevents unauthorized access |
| Distributed Learning | Keep data local, share insights only | Avoids cross-border transfers |
Each pattern involves trade-offs between performance, cost, and flexibility. The key is aligning architecture with risk tolerance and regulatory expectations.
Conclusion: Sovereignty Is a Design Decision, Not a Location Choice
Data sovereignty under GDPR has evolved. It is no longer a peripheral compliance task to be handled by checking a box for an EU data center. It is a core design constraint that must be woven into your infrastructure, vendor strategy, and data governance from the very beginning.
Organizations that continue to treat sovereignty as a simple problem of storage location will inevitably fall short of regulatory expectations and expose themselves to risk. In contrast, those that embrace it as an architectural principle enforcing control through technical and cryptographic means can build a foundation for both lasting compliance and secure innovation. The mandate from regulators is clear: stop trusting locations and start proving control.